A recently uncovered flaw in Microsoft’s Visual Studio Code (VS Code), a popular code editor and development platform, exposes stored authentication tokens to unauthorized access by malicious extensions on Windows, Linux, and macOS systems.
The vulnerability, found by cybersecurity firm Cycode, concerns the ‘Secret Storage’ functionality within VS Code, where tokens are kept for integration with services such as Git, GitHub, and other programming interfaces. A breach of these tokens may lead to unauthorized system infiltration, data leaks, or other cybersecurity incidents for the affected organizations.
Cycode’s researchers pinpointed the issue and developed a working proof-of-concept (PoC) to illustrate the flaw. Microsoft, however, declined to address the problem, reasoning that extensions within the platform are not meant to be isolated from the rest of the system environment.
Manipulating Extensions to Extract Secrets
The specific flaw at hand originates from the absence of proper isolation of authentication tokens in VS Code’s Secret Storage. The platform employs Keytar, a wrapper that communicates with credential managers on various operating systems, for storing tokens. Consequently, even malicious extensions can misuse this mechanism to gain access to stored tokens.
Cycode’s Alex Ilgayev explained that aside from built-in GitHub and Microsoft authentication, all stored tokens in VS Code could be accessed by third-party extensions, including those associated with widely-used platforms such as Git, Azure, Docker/Kubernetes, CircleCI, GitLab, and AWS.
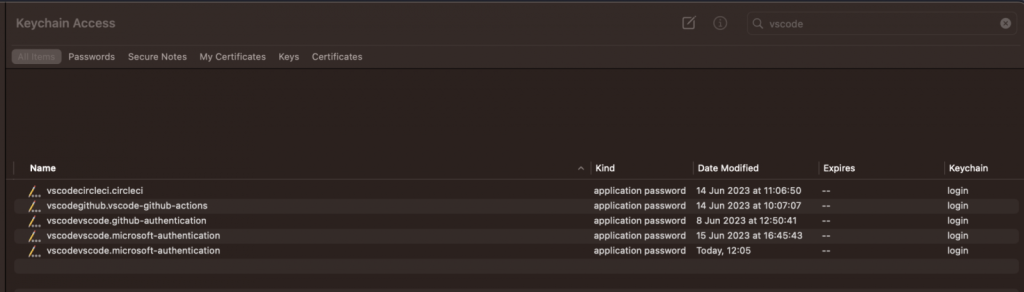
Keychain containing login passwords
Source: Cycode
Upon detecting this vulnerability, the researchers conducted experiments by creating a malicious extension to steal CircleCI tokens, gradually developing a more flexible attack strategy without altering the existing extension’s code. The discovery that any VS Code extension could access the keychain formed the cornerstone of this new method.
A Multi-faceted Issue
Furthermore, Cycode’s research revealed that the tokens could be decrypted using a custom JavaScript script, as the encryption key was derived from easily attainable information like the executable path and machine ID.
Additionally, a second flaw was identified where the ‘getFullKey’ function could be exploited, allowing attackers to impersonate other extensions and access their secure tokens.
Reaction and Implications
Cycode reported the findings to Microsoft two months prior, even showcasing their PoC extension. Despite these revelations, Microsoft’s development team chose not to see it as a security threat and continued with the existing design of VS Code’s secret storage management framework.
This decision has raised questions and concerns among some cybersecurity experts, as the vulnerability leaves room for potential exploitation by malicious entities. The overall impact of this issue remains to be seen, but organizations relying on VS Code are urged to be vigilant and aware of the risks involved.
Found this news interesting? Follow us on Twitter and Telegram to read more exclusive content we post.


